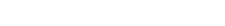
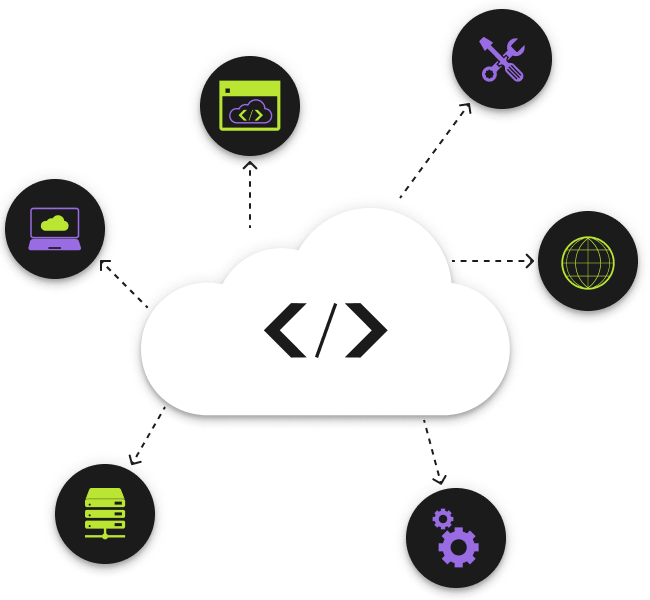
Cloud Hosting & Infastructure Management
Cloud is no longer a concept or a buzz-word. It’s a business necessity.
When we started hosting applications and websites, the cloud didn’t exist. From the early days of VMware and virtualization to the modern cloud, we’ve always been ahead of the curve. Today, our experience is vital in helping customers modernize and scale their hosting with the cloud.
Let’s talk cloud hosting.

On the tech side, we don’t miss the days of 3am pager alerts when the automated processes to roll logs restarted Apache and something didn’t come back up – which sometimes prompted a physical trip to the datacenter. If you’ve been in the IT trenches as long as we have you know what we’re talking about.
On the business side, before the cloud there was substantial business risk most managers didn’t even know about. Backups and redundancy were difficult and often not tested properly. Hardware is prone to failure and requires large capex. Software requires updates and managing traditional hosting is just expensive and exhausting.
There’s a better way, and it’s cloud hosting – and we can help.
AMY WARD Director of Organizational Effectiveness at Stan JohnsonTo be honest, we had a 5-year relationship with our previous website development / maintenance vendor going into the RFP process and while we wanted to do our due diligence, we fully expected that vendor would win the RFP bid. ABT came in and really wowed us and won our business. Atlantic BT helped us to identify the most impactful enhancements, which would align with our value proposition and growth strategy.
Our custom websites in action

Health industry .NET portal software development

Training company WordPress maintenance and support

DEA approved client portal redesign
Want to see examples of all our work?
Our Team of Experts
Our team is your powerhouse of expertise, ready to support and elevate your website, whether through a complete overhaul or targeted enhancements. Beyond our professional excellence, we value a harmonious balance between work and creativity. Visit our About Us page to meet the team. You’ll get a glimpse of our vibrant team culture through AI-generated profile pictures that showcase our ABTers in various imaginative avatars. It’s a fun peek into how we blend generative AI technology with our passion for innovative web design.

Seeking Enhanced Security
In an era where digital threats are becoming more sophisticated, the security of your data and applications is paramount. Many businesses are on the lookout for cloud hosting services that offer more than just storage; they need a fortress. Our cloud hosting solutions are designed with security at their core, equipped with advanced encryption, multi-layered security protocols, and continuous monitoring to thwart any threats. We understand the importance of your data’s integrity, and our commitment is to safeguard it with an unwavering dedication to robust security measures.
For Example:
Scenario 1
A healthcare provider experienced a data breach when sensitive patient records were exposed due to outdated firewall protections. The breach not only compromised patient trust but also resulted in hefty fines for non-compliance with HIPAA regulations.
Scenario 2
An e-commerce platform faced repeated DDoS attacks during peak shopping seasons, leading to extended downtime and significant revenue loss, highlighting the need for robust, proactive security measures.
Not sure where your project fits in?
Demand for High Reliability and Uptime
Your business’s online presence and operations are crucial, and even a minute of downtime can lead to significant losses. Recognizing this, companies seek cloud hosting vendors that can guarantee high availability and consistent performance. Our service level agreements (SLAs) are a testament to our promise of unparalleled uptime. With our state-of-the-art infrastructure and proactive incident resolution, we ensure that your digital assets are always available to your employees and customers, fostering trust and reliability.
For Example:
A financial services firm encountered frequent unplanned outages due to overloaded servers, causing disruptions in online trading platforms and affecting customer transactions and trust.
An online news portal struggled with website crashes during major news events due to traffic spikes, undermining their reputation for reliability at critical times.
Scalability and Flexibility Needs
As your business grows, so do your IT needs. The demand for a cloud hosting service that can seamlessly adapt to changing requirements is higher than ever. Our cloud solutions are inherently scalable, designed to provide you with the flexibility to upscale or downscale your resources according to your current business needs. This means you can adjust your IT expenditure based on demand, ensuring optimal efficiency and avoiding unnecessary costs.
For Example:
A rapidly growing online retail startup found its existing hosting solution couldn’t handle the increasing surge in traffic, leading to slow loading times and abandoned shopping carts during their most crucial sales period.
A gaming company releasing a new online multiplayer game faced challenges in scaling their infrastructure quickly to accommodate the influx of new users, resulting in lag and user dissatisfaction.
Cost-Effective Resource Management
One of the primary motivators for businesses shifting to cloud hosting is the potential for significant cost savings. Managing an in-house IT infrastructure is not only costly but also resource-intensive. Our cloud hosting services eliminate the need for large upfront investments in hardware, reduce ongoing operational costs, and diminish the financial burden of regular maintenance and upgrades. By partnering with us, you benefit from a predictable OPEX model while enjoying access to the latest technologies.
For Example:
A small but expanding marketing agency realized they were over-investing in on-premises hardware that was underutilized outside of peak campaign periods, signaling a need for a more flexible, cost-effective cloud solution.
An independent software developer found maintaining their own servers for app hosting was becoming prohibitively expensive, especially when factoring in the sporadic nature of user demand and the cost of emergency repairs.
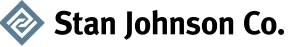
Expertise and Specialized Support
The intricacies of cloud environments require a level of expertise that can be challenging to cultivate in-house. Companies are thus on the lookout for a cloud hosting partner that brings a wealth of knowledge and specialized skills to the table. Our team of cloud experts is at the forefront of industry best practices, equipped to manage your hosting environment efficiently. With round-the-clock support, we ensure that any issues are promptly resolved, minimizing any potential impact on your business operations.
For Example:
A legal firm lacking in IT expertise faced significant challenges in managing their client data securely in the cloud, leading to potential confidentiality breaches and inefficiencies in data retrieval.
An educational institution wanted to migrate to the cloud but was overwhelmed by the complexity of their legacy systems and the specialized knowledge required to ensure a smooth transition.
Compliance and Data Protection
Navigating the complex landscape of compliance regulations is a daunting task for many businesses. This challenge is compounded when dealing with sensitive data and the need to adhere to stringent industry standards and laws. Our cloud hosting services are designed with compliance at their core, ensuring that your data is managed in accordance with relevant regulations. From GDPR to HIPAA, we have the expertise to ensure your cloud environment aligns with legal requirements, providing peace of mind and safeguarding your reputation.
For Example:
A pharmaceutical company, under scrutiny for regulatory compliance, struggled with maintaining data integrity and secure access controls, risking severe penalties and loss of license.
A finance company faced challenges with international data sovereignty laws, as their data hosting solution didn’t automatically adapt to the geographic regulations, putting them at risk of legal issues.
Focus on Core Business Functions
In today’s competitive market, businesses must focus on innovation and core competencies to thrive. Outsourcing your cloud hosting to a trusted partner allows your team to concentrate on what they do best, without being bogged down by the complexities of IT infrastructure management. Our managed cloud services provide you with the freedom to innovate, safe in the knowledge that your cloud infrastructure is in expert hands, running smoothly, securely, and efficiently.
For Example:
A real estate agency found their internal resources were excessively tied up in managing IT infrastructure, detracting from their primary focus of client service and property management.
A manufacturing firm wanted to digitize their operations but realized that their core team’s efforts were better spent on innovation and product development rather than IT maintenance.

Transitioning to the Cloud
For many organizations, moving to the cloud represents a significant shift in their IT strategy, often driven by the need for digital transformation. Whether you are migrating from an on-premise data center or transitioning from another cloud provider, the journey to our cloud hosting service is designed to be as smooth and seamless as possible. We understand the challenges that come with such a transition, including concerns about data loss, downtime, and security. Our comprehensive migration strategy ensures a secure, efficient, and timely move to your new cloud environment, empowering your business to leverage the full benefits of cloud technology without the hassle.
For Example:
A local government entity faced public scrutiny after an outdated server system led to a prolonged service outage, affecting public access to essential services and information.
A media company with a global audience suffered from inconsistent content delivery speeds due to reliance on a single-location server, necessitating a move to a distributed cloud model to maintain viewer satisfaction.