Our Solutions
Transforming your ideas into real business results
We’ve been around for more than 25 years and as we’ve matured we’ve learned what we’re really, really good at, and what others can do better. When we’re a good fit for your team and your organization, together we can do amazing things.
Let’s talk.

Our Solutions
We offer a specific set of skills on various platforms to best suit your individual, unique needs.
Core expertise
Our services revolve around four core areas of expertise. While our offerings evolve with the digital landscape, these pillars remain central to our mission.
Websites & Portals
Atlantic BT’s website and portal development delivers dynamic, secure, and user-focused digital experiences.
Software
Elevate your business with Atlantic BT’s custom software development – bespoke solutions to drive growth, efficiency, and innovation.
Cloud
Transform your business with our custom cloud solutions, leveraging cloud hosting and management alongside software-as-a-service.
AI
Unlock AI’s potential with our expert consulting, delivering tailored strategies, quick wins, and deep integration to revolutionize your operations.
Our website development process
We’ve mastered the art of flawless delivery
Discovery
Design
Deploy
Want to see everything Atlantic BT has to offer? Check out our full process.
Our Work
See our experience in action.

AI consulting for HVAC company
Comfort Monster turned to Atlantic BT for HVAC AI consulting to find out how AI could best be integrated into their existing processes.

B2C WordPress Web Design Improvement
LifeSafer helped launch the ignition interlock industry and needed their B2C WordPress web design to match the same ease of use.

DEA approved client portal redesign
Mutual Drug relied on Atlantic BT as their technology partner to ensure secure digital operations for their billion-dollar pharmacy business.
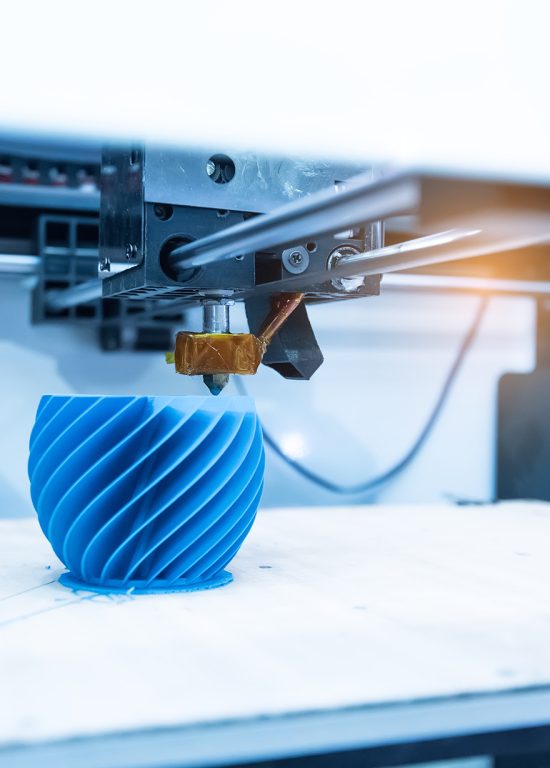
Digital Manufacturing Web Design
Facing the need for manufacturing web design to accommodate escalating enterprise demands, Shapeways collaborated with Atlantic BT.

Custom website and partnership with b2b technology company
Toshiba Global Commerce collaborated with ABT to redesign their custom b2b website, resulting in a Silver Stevie® Award.