Good DevOps practices ensure that the same code bundle can be deployed into multiple environments and environment-specific elements can be automatically injected from outside the code bundles themselves.” -Bernard Golden, Author and CEO of Navica
Golden describes just one example of how DevOps delivers significant improvements in development speed and agility. By increasing cooperation between IT engineers and developers, DevOps streamlines workflows across a software project. This has made DevOps a popular approach for many IT leaders.
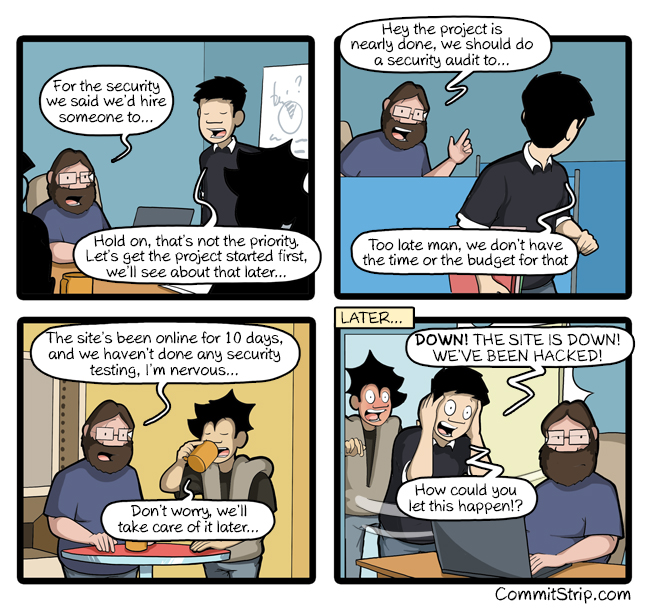
However, with all of this increased speed it is easy to view security concerns as inhibitors to DevOps agility. After all, if your developers are nailing their deadlines and your IT engineers are creating rock-solid environments for your software, why would you want worries about security to slow down your incredible progress? As the CommitStrip below amusingly points out, security doesn’t seem like a major concern until something goes wrong. And then, it may be too late to stop the issue from bringing down the entire application or system.
Question: When Should You Integrate Security into DevOps?
Answer: Yesterday.
Information security architects must integrate security at multiple points into DevOps workflows in a collaborative way that is largely transparent to developers, and preserves the teamwork, agility and speed of DevOps and agile development environments, delivering ‘DevSecOps.’” -Gartner 2016 report
It is not enough to add on patchwork security protocols or systems just before deployment. Nor can you simply recruit a security expert to check your developers’ code as they work. To truly integrate security throughout your workflows, you need to ensure your developers are a transparent part of the security process. In short, stay true to the collaborative spirit of DevOps.
This is not easy. Modern security infrastructure has lagged in its ability to become “software defined” and programmable, making it difficult to integrate security controls into DevOps-style workflows in an automated, transparent way. In addition, because developers often download and use open-source components and frameworks, modern applications are largely “assembled,” rather than developed from scratch. This creates application security issues as many of these open-source additions are vulnerable to cyberattack.
SecDevOps Training, Tools, and Best Practices
So how can you stay true to the collaborative vision of DevOps as you weave security into your development processes? Information security architects should take the lead by adopting the following tactics to create a strategic SecDevOps approach:
- Start with secure development and training. This does not mean you need to force your developers to become security experts or adapt an entirely new set of tools, but introducing the right secure practices can safeguard your software. For example, you should create deployment pipelines that allow for controlled code pushes into the production environment; by using Red/Black deployments, you can transition to the updated code running on the new infrastructure with zero impact to sessions, transactions, or the user experience. When scanning platforms, the Nessus product, from Tenable Security, can improve security without impacting your workflow.
- Embrace the concept of people-centric security. Beyond training, this means empowering developers to take personal responsibility for security by encouraging a “trust and verify” mindset. Note that monitoring your systems is still important, but you need every team member to take ownership.
- Require all information security platforms to expose full functionality via APIs for automatability. By automating regular code tests, you help ensure your software will be secure without demanding more effort from your team.
- Use proven version control practices and tools for all application software and, equally as important, for all scripts, templates and blueprints used in DevOps environments. A GIT branching model is also helpful while writing code.
- Adopt an immutable infrastructure mindset. Rather than focusing on maintaining and improving, your data center’s individual machine uptime, an immutable infrastructure relies on API-driven infrastructure-as-code. This improves flexibility by letting you lock down and change production systems via development.
Learn More about SecDevOps Training
This is only an introduction for how you can integrate a security mindset into your DevOps practices. If you’d like to learn more about best practices and tools to secure your applications and systems during development, contact our security team here at Atlantic BT. We know all of the ins and outs necessary to guide you to confidence and safety.
With these best practices and more, you will be well on your way to delivering secure-by-design software that integrates effectively with your chosen platforms.