In a fast-evolving world, data is essential to good decision making. This makes accessibility paramount AND the utmost security is the universal expectation. What a paradox we’ve created.
Data is valuable because of the insights we can derive from it. But, we must also make sure data stays secure to protect privacy. A flexible governance approach maximizes data across an organization.
What does this approach look like? It’s the incorporation of proper user access control and/or role-based access to data. Vital to this data access is its classification.
Being an agency, ABT employees have access to many sources of data. We work with all types of clients and industries. Once we have access, we are usually held accountable for what happens to this data while it’s in our possession.
In our case, data is only accessible by the relevant department. For instance, the passwords for client WordPress sites are only given to developers and marketers. This isn’t the case for all data in our organization. Data with a high risk potential is more strictly guarded. Our data governance process is one that is reliable and effective.
Defining Data Governance
Data governance is not a ‘one size fits all’ system. Your organization will need its own unique strategy. Small organizations can afford to grant data access to users faster, due to size. Bigger organizations should follow a more rigid process.
The Data Governance Framework laid out by the Data Governance Institute is a good place to start. They describe this framework as a “logical structure” for data organization and activities. This is especially true with regards to “making decisions and taking action on…data.”
Applying this framework assigns rigorous accountability. It also provides a clear process for making decisions. But, it does have a drawback. This kind of strict governance leaves little room for flexibility.
Unfortunately, rigidity slows down decision making. Strict processes can have a monetary impact on an organization in the short term.
Better Governance through Data Classification
To strike the right balance, consider the classification of your data. Not all data is equal, so not all data needs to adhere to the strictest of controls. How do you know the difference? What data needs high levels of governance vs standard governance?
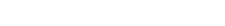
At Atlantic BT, we refer to the Federal Information Processing Standards. This document covers the categorization of information. It also covers information systems as seen in this chart:
An informal governance framework will be best for data that is low risk. The odds of it compromising confidentiality and integrity are small. This kind of data does not need to follow strict governance for user access. Stakeholders can then access this data with ease. As a result, faster and better decisions can occur with minimal risk.
Who has access to what data?
A subset of governance is security through user access controls. User access controls are like role-based access. There are restrictions to data with regards to who actually needs to use/see it. For example: marketer 1 works for client A but not client B, so she has access to analytics data for A’s campaign but not B’s. Likewise, marketer 2 works for client B but not A and so he doesn’t have access to client A’s data.
One way to achieve this level of security is through a data access policy engine. These tools allow you to give users access to the exact data needed to do a specific job and nothing else. You can grant access to more information as projects get transferred or the team adds a new member. Even better, you can do all this faster. Granting access can be as informal as sending an instant message to a data steward. There is a caveat. The data steward has a tough spot to fill. They must have a general understanding of every employee’s role. It’s the only way they can determine if an employee needs the information to complete a job.
A more specific aspect of user access controls are role-based access controls. These are specific to an employee of an organization where access to data is dependent on a combination of department, location, and job title. Just like with user access controls, you can govern these through an informal structure to decrease the steps someone might have to go through to access data. Again, this should only be applied to data that has a low potential impact for an organization in case that data is compromised.
Finding the Right Governance Fit
In conclusion, a minor sacrifice in governance (not security) can help resolve the tension of having your data be as secure as possible while also maximizing the accessibility of that data.
However, this fix can’t work for everyone. Larger organizations might have trouble incorporating a system like this, since a data administrator or data steward does not work closely with everybody, making it difficult to have a general understanding of every employee’s role. Additionally, multinational organizations might have to adhere to country-specific requirements that impede them from sharing data across offices or countries.
Start a conversation with us. We can answer any questions you may have on data governance or access.